CrowdStrike Event Stream
The CrowdStrike Event Stream provides a continuous flow of real-time security events and telemetry data generated by the CrowdStrike Falcon platform. This stream captures critical information such as detected threats, endpoint activity, and alert notifications. Organizations can leverage the Event Stream for immediate threat analysis, integrating with SIEM systems, or creating custom dashboards for enhanced visibility and response to security incidents.
CrowdStrike logs are ingested by utilizing the CrowdStrike streaming events service that they offer. Every 60 seconds we connect to your CrowsStrike event streams and ingest any events that are forwarded.
Setup
Login to your CrowdStrike account and navigate to API clients and keys under the Support and resources section.

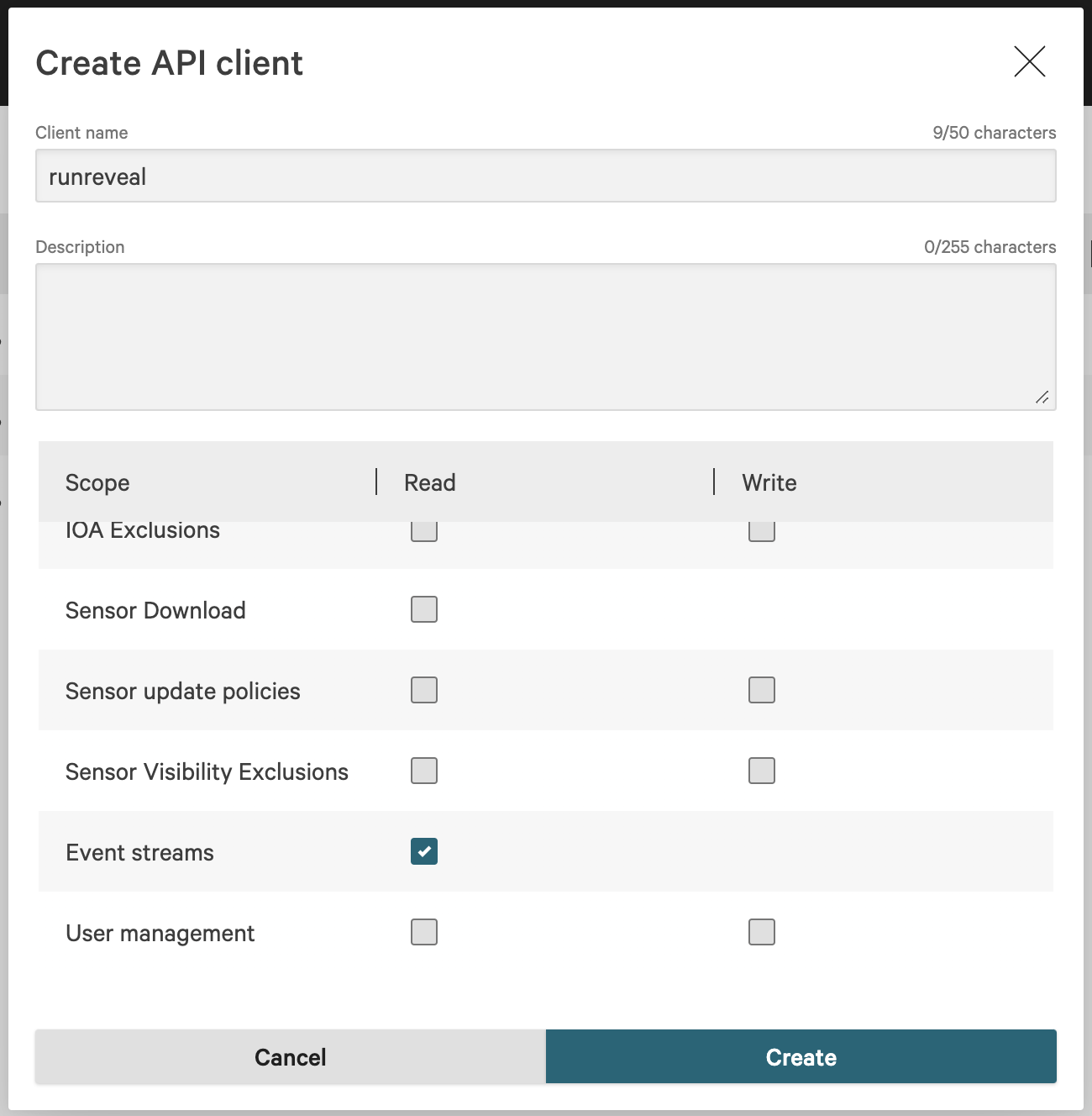
Create a new OAuth2 API Client from this page. Give the client a name and optional description. RunReveal only requires Read access to Event Streams for ingestion to work.
Save the Client ID, Client Secret, and Base URL that is displayed once created. You will need these when setting up your RunReveal source.

In RunReveal, create a new CrowdStrike source. Give it a name and fill in the values from your API client.
Once added CrowdStrike events should start ingesting within a few minutes.
The default Event Streams: Read scope is the minimum required to ingest streaming events. The optional EDR alerts endpoint described below requires an additional scope on the same API key.
Optional: EDR Alerts
The CrowdStrike source can additionally poll the Falcon v2 alerts endpoint, which returns richer detection data than the streaming feed alone.
| Toggle | Endpoint | Required scope | What it provides |
|---|---|---|---|
| Enable EDR Alerts | POST /alerts/entities/alerts/v2 | Alerts: Read | Full v2 alert payloads with MITRE ATT&CK mappings, ThreatGraph indicators, process lineage (parent + child with SHA256, cmdline, user SID), and a direct falcon_host_link for console pivot. |
To enable this, edit your CrowdStrike API key in the Falcon console and grant the Alerts: Read scope, then toggle Enable EDR Alerts on the source settings page.
EDR alert events land in the same crowdstrike_event_logs table as streaming events and can be distinguished by serviceName = 'crowdstrike-alerts'.
If the toggle is enabled but the API key lacks the Alerts: Read scope, the source logs a warning each poll cycle and skips the alerts endpoint — streaming events continue to flow.
Schema
The following columns are exposed for this source. RunReveal applies schema normalization across all sources, ensuring uniform field names and data types for cross-source queries and reusable detection logic.
Table: crowdstrike_event_logs (49 columns)
crowdstrike_event_logs (49 columns)| Column | Type |
|---|---|
workspaceID | String |
sourceID | String |
sourceType | String |
sourceTTL | UInt32 |
receivedAt | DateTime |
id | String |
eventTime | DateTime |
eventName | String |
eventID | String |
srcIP | String |
srcASCountryCode | String |
srcASNumber | UInt32 |
srcASOrganization | String |
srcCity | String |
srcConnectionType | String |
srcISP | String |
srcLatitude | Float64 |
srcLongitude | Float64 |
srcUserType | String |
dstIP | String |
dstASCountryCode | String |
dstASNumber | UInt32 |
dstASOrganization | String |
dstCity | String |
dstConnectionType | String |
| Column | Type |
|---|---|
dstISP | String |
dstLatitude | Float64 |
dstLongitude | Float64 |
dstUserType | String |
actor | Map(String, String) |
tags | Map(String, String) |
resources | Array(String) |
serviceName | String |
enrichments | Array(Tuple(data Map(String, String), name String, provider String, type String, value String)) |
readOnly | Bool |
rawLog | String |
success | Bool |
utcTimestamp | DateTime |
message | String |
source | String |
apiClientId | String |
cid | String |
requestMethod | String |
requestPath | String |
statusCode | String |
userAgent | String |
traceId | String |
elapsedMicroseconds | String |
region | String |