Webhooks
RunReveal sends an HTTP POST request to a URL of your choosing whenever a detection fires, a test is triggered, or another notification event occurs.
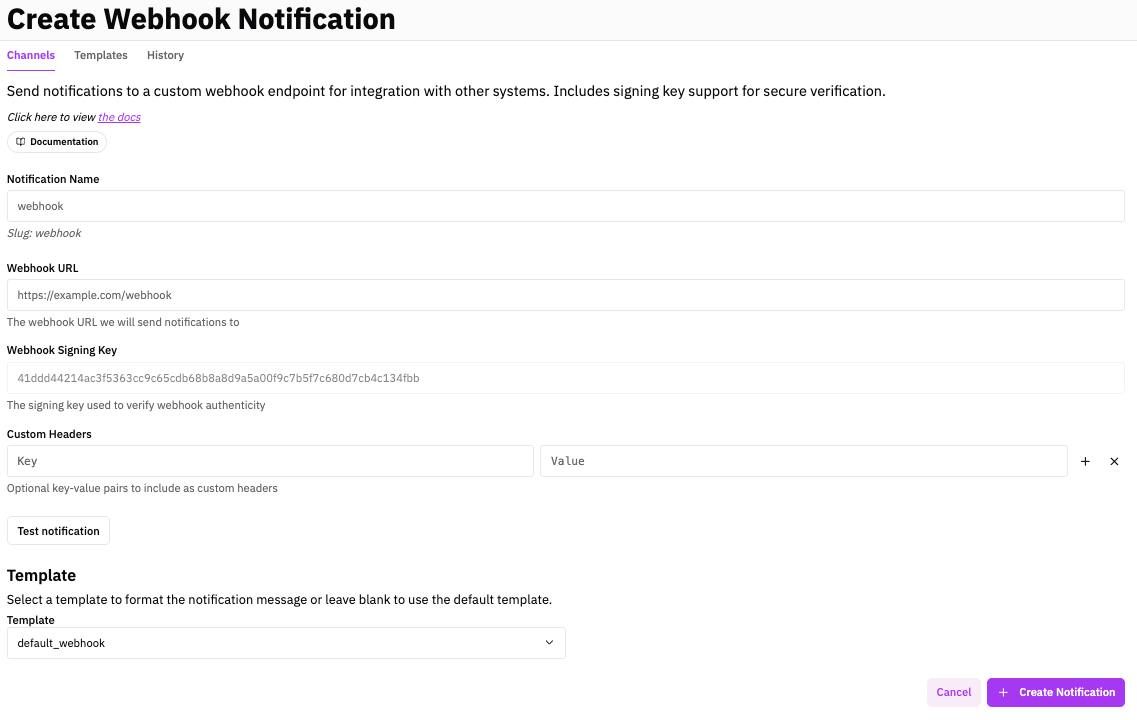
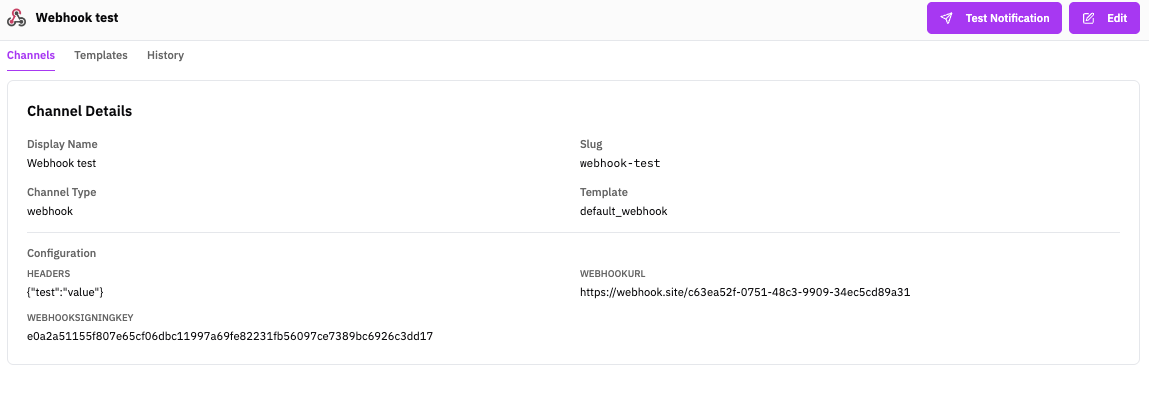
Set this up from the Notifications page in the RunReveal dashboard.
Payload Schema
Every webhook POST body is a JSON object with these top-level fields:
| Field | Type | Description |
|---|---|---|
title | string | Rendered notification title (from template). |
body | string | Rendered notification body (from template). |
channel | string | Notification channel type — always "webhook" for this channel. |
detection | object | Present for detection alerts. See Detection object. |
test | object | Present for test notifications (e.g. {"status": true}). |
data | object | Present for other event types (health checks, user activity, etc.). |
Example payloads
Detection object
All detection types share these common fields:
| Field | Type | Description |
|---|---|---|
id | string | Unique execution / alert ID. |
detectionID | string | The detection rule's ID. |
workspaceID | string | Workspace that owns the detection. |
name | string | Machine-readable detection name. |
displayName | string | Human-readable detection name. |
detectionType | string | "query", "stream", "agent", or "health". |
severity | string | "low", "medium", "high", or "critical". |
riskScore | number | Numeric risk score (0–100). |
categories | string[] | Detection categories. |
mitreAttacks | string[] | MITRE ATT&CK technique IDs. |
mitreTechniques | string[] | MITRE technique names. |
description | string | Detection description. |
notes | string | Optional analyst notes. |
system | boolean | true for managed detections. |
executedAt | string | ISO 8601 execution timestamp. |
triggered | boolean | Whether the detection triggered an alert. |
resultLink | string | Direct link to the alert in RunReveal. |
error | string | Error message, if execution failed. |
Additional fields depend on the detection type:
| Field | Type | Description |
|---|---|---|
query | string | The SQL query text. |
params | object | Query parameters (from, to, window). |
runTime | number | Execution time in milliseconds. |
resultCount | number | Number of result rows. |
nextRunTime | string | Next scheduled execution (ISO 8601). |
prevRunTime | string | Previous execution (ISO 8601). |
results | object[] | Row-oriented result objects (each row includes __alertID__, __columns__, and data fields). |
columns | string[] | Column / field names. |
values | any[][] | Columnar result data. |
Webhook Signing
Signing is optional. If no signing key is configured, the RunReveal-Integrity header will contain RUNREVEAL_MESSAGE_UNSIGNED.
When a webhook signing key is set, RunReveal signs every request (including test notifications) so you can verify authenticity.
Headers
| Header | Description |
|---|---|
RunReveal-Timestamp | Unix timestamp (seconds) when the webhook was generated. |
RunReveal-Integrity | Base64-encoded HMAC-SHA256 signature, or RUNREVEAL_MESSAGE_UNSIGNED. |
How to verify
Capture the raw request
Read the RunReveal-Timestamp header and the raw HTTP request body bytes. Do not parse the JSON first.
Build the signed payload
Concatenate the timestamp string and the raw body (no separator): <timestamp><body>
Compute the HMAC
Hex-decode your signing key to bytes, then compute HMAC-SHA256 over the concatenated payload. Base64-encode the result.
Compare
Compare your computed signature with the RunReveal-Integrity header using a constant-time comparison.
Verification examples
The following examples include a junk key for demonstration only. Copy and run the test to confirm your verification logic matches RunReveal's.
Signatures are calculated for test notifications too, so you can verify your implementation before going to production.
Related
- Getting Started with Notifications — Set up channels and add to detections
- Notification Channels — All channel types
- Notification Templates — Customize payload content
- Detections — Attach channels to detection rules