Okta Security Logs
Okta Security logs allow you to view audit events from your Okta admin dashboard as well as user authentication attempts.
Okta stores 30 days worth of logs for your account, when adding the Okta source, we will backfill your account with whatever logs Okta has available. After the initial load, RunReveal will attempt to poll the Okta API to download your security logs every 60 seconds.
Setup
Give your Okta source a descriptive name to help find it later. The two fields we require from your Okta account are your Okta domain and an API token. Your Okta domain is the domain that was assigned to your Org.
Okta Domain
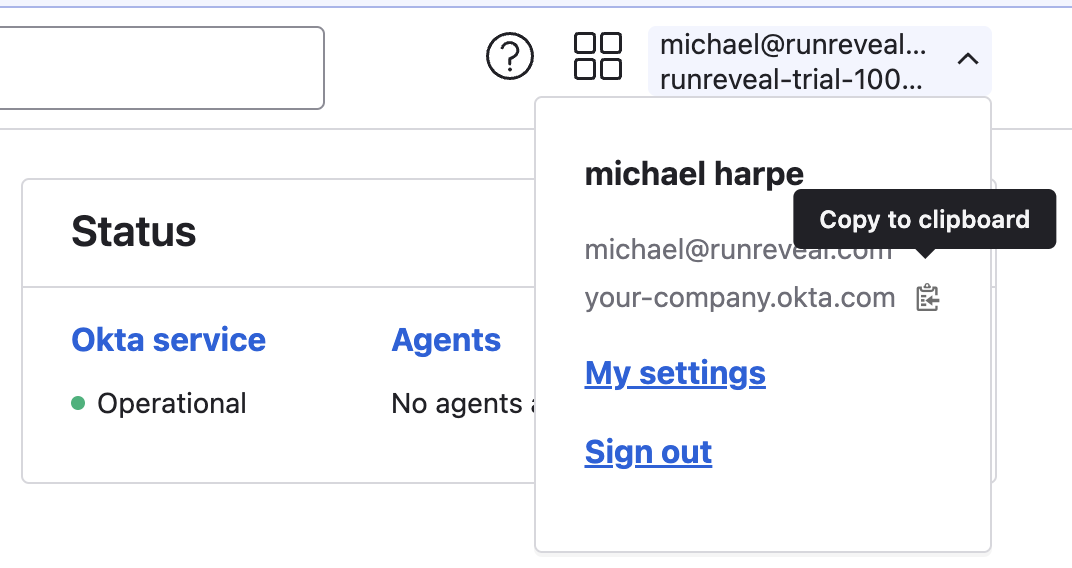
To find your Okta domain:
- Sign in to your Okta org admin dashboard.
- Look in the header under your profile dropdown.
- Click the copy button and paste the results into RunReveal.
Your Okta domain may look like one of the ones below. When pasting your domain, make sure it does not have -admin and do not include trailing slashes or the schema https://
example.oktapreview.comexample.okta.comexample.okta-emea.com
API Token
An API token is required to authorize RunReveal to access your Okta logs. API tokens remain active as long as they are being used. If a token is unused for 30 days it will be revoked by Okta and a new one must be issued. API tokens must be linked to an active Okta user. When a user is removed all of the API tokens they created will be revoked and a new one will need to be generated.
To generate a new token, from your Okta admin dashboard, open the Security -> API page in the lefthand navigation panel. Click on the Tokens option and you will be presented with a list of all of your API tokens. Click the "Create Token" button and enter a descriptive name for your token, like "RunReveal". You will be presented with your token value, copy this value and paste it into RunReveal.
Okta API tokens are scoped to the user creating them. For additional security consider creating a new user with lower permissions and generating an API token from that account.
Verify Its working
Once added the source logs should begin flowing within a minute.
You can validate we are receiving your logs by running the following SQL query.
Schema
The following columns are exposed for this source. RunReveal applies schema normalization across all sources, ensuring uniform field names and data types for cross-source queries and reusable detection logic.
Table: okta_logs (66 columns)
okta_logs (66 columns)| Column | Type |
|---|---|
workspaceID | String |
sourceID | String |
sourceType | LowCardinality(String) |
sourceTTL | UInt32 |
receivedAt | DateTime |
id | String |
eventTime | DateTime |
eventName | String |
eventID | String |
srcIP | String |
srcASCountryCode | String |
srcASNumber | UInt32 |
srcASOrganization | String |
srcCity | String |
srcConnectionType | String |
srcISP | String |
srcLatitude | Float64 |
srcLongitude | Float64 |
srcUserType | String |
dstIP | String |
dstASCountryCode | String |
dstASNumber | UInt32 |
dstASOrganization | String |
dstCity | String |
dstConnectionType | String |
dstISP | String |
dstLatitude | Float64 |
dstLongitude | Float64 |
dstUserType | String |
actor | Map(String, String) |
tags | Map(String, String) |
resources | Array(String) |
serviceName | String |
| Column | Type |
|---|---|
enrichments | Array(Tuple(data Map(String, String), name String, provider String, type String, value String)) |
readOnly | Bool |
rawLog | String |
published | DateTime |
eventType | String |
legacyEventType | String |
displayMessage | String |
uuid | String |
outcome | String |
severity | String |
srcDomain | String |
srcGeoLocation | String |
srcPostalCode | String |
srcState | String |
actor.alternateID | String |
actor.displayName | String |
actor.id | String |
actor.type | String |
client.device | String |
client.userAgent | String |
client.os | String |
client.browser | String |
client.zone | String |
target | Array(String) |
request.ipChain | Array(String) |
authenticationContext | String |
debugContext | String |
transaction.id | String |
transaction.type | String |
debugContext.debugData | String |
debugContext.debugData.risk | String |
debugContext.debugData.threatSuspected | String |
debugContext.debugData.behaviors | String |